
Let’s discover Actions, those pieces of code that act as flexible extensions to the authorization and authentication flow!
For starters, what’s Auth0 ?
Auth0 is an IaaS (Identity as a Service) solution, designed by and for developers. Acquired by Okta in 2021, Auth0 will become the solution for CIAM (Customer Identity Access Management), while the Okta platform will focus on WIAM (Workforce Identity Access Management).

You therefore have access to centralized management of your applications, authorization servers (referred to as APIs in an Auth0 tenant), and authentication channels (copyright Point Base’s boss, Christian Fourneau, I really like this terminology he uses to designate “connections” in the Auth0 tenant).
Implementing authentication and authorization in an application with Auth0 will take about 5 minutes, and a few lines of code. In fact, over 30 SDKs (Software Development Kits) are available to enable you to add Auth0 to your application, whatever the language (JS, PHP, Java, Python…) or framework (Vue.JS, React, Angular as examples for the front end, Node, Go, Laravel for the back end). IOS and Native developments are also covered.
In short, Auth0 is the CIAM / IaaS solution that makes your life easier, but above all provides you with the technical means to secure access to your resources via robust authorization protocols such as OAuth 2.1 , OIDC (OpenID COnnect) or SAML (Security Assertion Markup Language), or the addition of social Identity Providers (Facebook, LinkedIn, Twitter…). And I’m only mentioning a small portion of the existing possibilities for authentication channels.

OK then. And what about Actions ?
If you’re here, your curiosity must have been piqued. Good, because you won’t be disappointed. There are two types of Actions: those from the Marketplace and custom Actions.
Custom Actions : code your own logic !
Custom Actions are pieces of code written in Node.JS, stored in a library on the Auth0 tenant, and which are injected into one of the Auth0 flows: authentication, machine-to-machine, pre- or post-registration of a user, after password change, or SMS sending in the MFA (Multi-Factor Authentication) framework.

The aim of these Actions? To enable you to add custom logic that meets your needs, probably common to several of your applications, without having to write the same code in each application.
A few examples wouldn’t go amiss…
Readers, I hear you.
Let’s imagine you have two applications that may need to talk to each other and exchange data: you’ll most likely need certain information to appear in the custom claims of your ID token or Access Token. Rather than writing code in each application, Auth0 lets you use an Action to enrich the targeted token with a custom claim whose name and value you define. Want something concrete? Here it is:

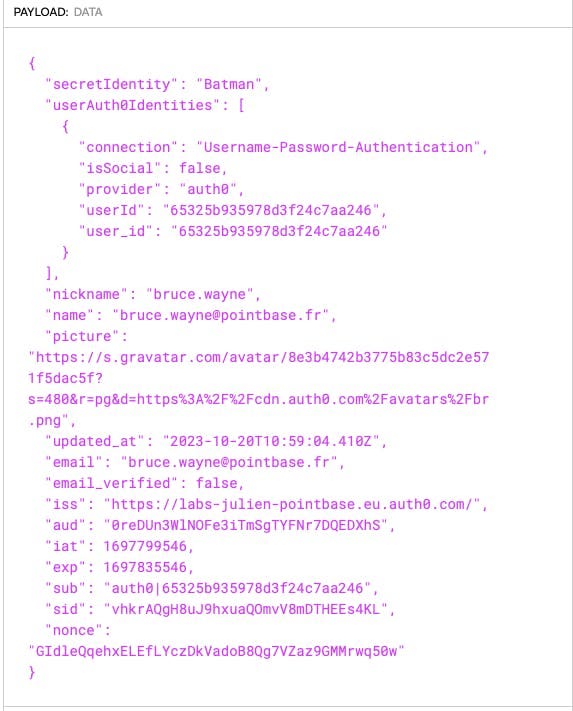
Here, when an authorization takes place, the action will add four pieces of information via the API object:
- an “email” claim in the Access token (line 9), based on the context of the authenticating user
- an “emailVerified” claim in the Access token (line 10), which does the same to retrieve the value in the Auth0 profile of the “email_verified” attribute
- a “secretIdentity” claim in the ID token with the static value “Batman” (line 11)
- and finally, a “userAuth0Identities” claim, also in the token ID, which returns an array of the various Identity providers listed for the user in Auth0. The next step? Click on “Deploy” and, above all, add this action to the Login flow, so that it runs as soon as the user logs in, and before the token is supplied to the application. Finally, click on “Apply”.

Here is the result :

Note that you can chain Actions one after the other in flows.

Here, for example, an initial Action Guardian MFA checks whether the user attempting to connect to the application is in Europe. If so, he or she is required to use the MFA Guardian application to provide an OTP code or validate a push notification. The token is then enriched before being sent to the application.
Want another example of Custom Action? Let’s take a “Post User registration” flow. For a case where you want a new user to be registered on the connection named “customers”, a new line is added to a google spreadsheet. You code your condition, pass a call via the axios library into your action, and you’re done:

That’s a lot of possibilities, isn’t it?
What about the second type of Action?
If you don’t feel like or need to code your own Action, you can also check out Auth0’s marketplace, which offers a number of available, pre-built Actions that only need local configuration in your tenant to apply.

Incidentally, I’d like to draw your attention to an extremely interesting Action, which can complement your CIAM management with Auth0: the possibility of using Okta workflows if you have a WIC (Workforce Identity Cloud) tenant. In this case, you can use a workflow triggered by an Endpoint API card, from which you retrieve the invoke URL and Token client.

You can pass certain properties of the event object as data sent to the workflow:

If this isn’t further proof of the complementary nature of Okta and Auth0, I don’t know what more you need!
Finally, the Actions all run in the order you specify, regardless of whether they are custom Actions or Actions installed from the Marketplace. So don’t hesitate to combine these two types of Actions to achieve the Auth0 customization objective you’re aiming for, in line with your needs.
Things to remember
- Auth0 Actions are pieces of code that you either write yourself, or import from the Auth0 Marketplace.
- They are executed in the order you configure within one of the available flows.
- In a Custom Action, you can call up an npm package and define secrets. You can even test an execution
- Each flow provides access to properties related to event and/or api objects.
- The number of Actions depends on your plan (Free: 3, Essential: 5, Professional: 7, Enterprise: unlimited).
- Actions are designed to enable you to add your own specific logic to Auth0’s CIAM management.
- Actions are great!
Of course, what I’ve done here is give you a fairly simple overview of all the possibilities offered by Actions. For more configuration details, and examples of common use-cases for Actions, I encourage you to consult the documentation here.

 IAMSE
IAMSE