One of the many automation use cases that Okta brings to the Microsoft ecosystem is its capability to manage the lifecycle of identities. In this Article I will guide you how to provision and deprovision Office 365 Guest accounts automatically when a user gets onboarded until their offboarding as an exemple, leveraging Okta Workflows and the Microsoft Grap API.
Prerequisites:
- 1 x Okta Workforce Identity tenant (Trial available here).
- 1 x Okta Workflows tenant (Provisioned with above tenant – 5 Free Flows included).
- 1 x Office 365 / AzureAD tenant with users and basics licencing E3 or developer account.
- Basic Knowledges of Okta Admin Console, Workflows and Office365&Azure AD.
Azure AD Application Configuration:
In order to be able to make an API call from Workflows to the Microsoft graph API we will need to create an Oauth Application in your Azure AD Tenant.
Go to your Azure Active Directory tenant and click on the left menu onto Register an Applications. As per below screenshot click onto “New Application”.
Select as per screenshot and add the redirect URL: https://oauth.workflows.okta.com/oauth/httpfunctions/cb
Click Register to create your Application.

Now your new Application is created we now have to configure the API Permission
Back to your Azure Active Directory dashboard go to App Registration then select “All Applications” and click on your Application:

On the left menu click now on “API Permission” then click on “Add a permission” and select “Mircosoft Graph” then “Application permissions”

Looks for the User section and select “User.ReadWrite.All” and click “Add Permissions”

Once the permission is added click onto Grant admin consent for your Azure AD tenant.

Next step and still within your App Registration section click on “Authentication” and make sure to select “Access Tokens” and “ID Tokens”. Click “Save”.

Next step require to create a client secret for our Application. From the same dashboard go to Certificate&secrets and click “New client secret”.
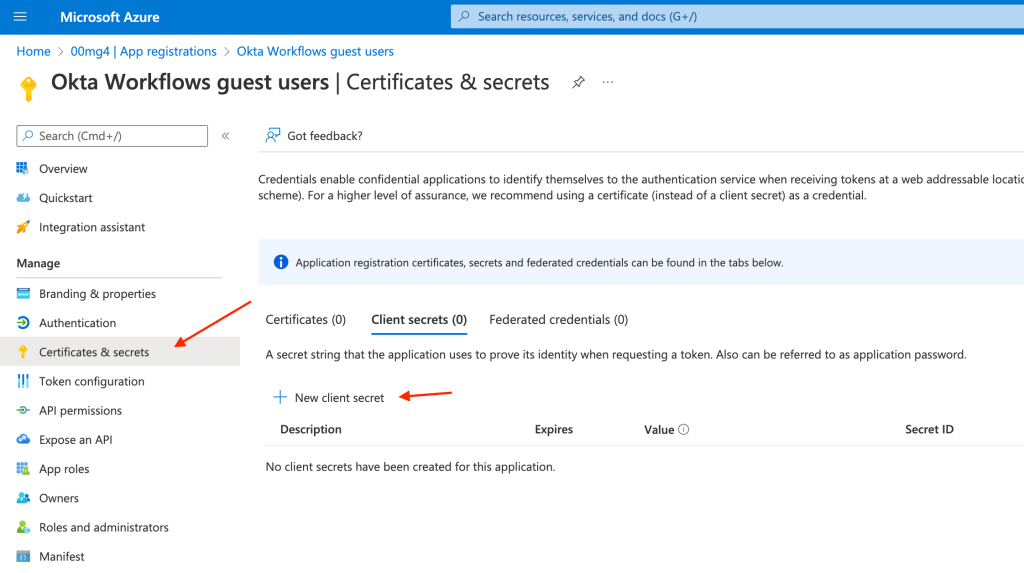
Give the secret a name and a period and click save.
Make sure to copy/save the secret value to be used later in this article.

Okta Workflows configuration
To make it a lot easier we are providing the Flowpack that is available on our Github repository here.
Download the Flowpack and import it to Okta Workflows. In the Okta Workflows console click the little setting icon and click import. Select the file.folder and import it.

You will be then presented with the flowpack below:

You will now need to go into these flows one by one and make sure the card are connected properly. if you did connect Worflows to your Okta tenant prior the Okta Card will automatically pick up the connector configuration. If you haven’t connected it please follow the link.
Now we need to create a new connection for our API cards that are located in our [util] flows. In Workflows Console go to connections then new connection.

Give it the name you like and Auth type must be set to None. Click Save.
Go back to your Flows [Util] and in all of them make sure to select your API Connector you created and hit save.

We need now to add the Azure AD Credential to our Table

Once in the table please type in each row under name and value field.
tenant_id = Azure AD ID can be found at the overviews dashboard of your Azure AD.
client_secret = Past from previously created
client_id = The Application Client ID from the app you created

Now go back to your flow and turn them all on. Please check through the different cards/flow that everything is configured.

As you can see we have design this flow to create a guest accout when an Okta user gets added to the O365Guest group and then deleted when the user gets removed from it. Please create the group in your Okta tenant for testing.
Now if you add a user to the O365Guest group you will see that the user gets created into Microsoft Azure as a guest.
You can now confirm the creation and deletion of guest users automatically.

Special credit to Mark Smith for his continuous Worflows support.

 IAMSE
IAMSE